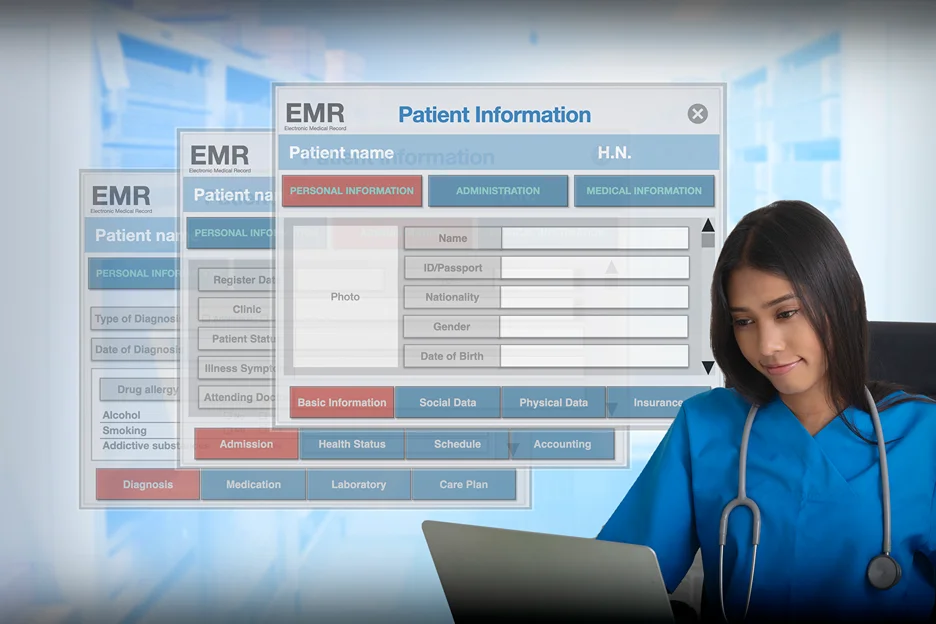
Electronic medical records (EMRs) have revolutionized the way healthcare providers store and access patient information. EMRs are digital versions of traditional paper-based medical records that contain detailed information on a patient's medical history, medications, allergies, lab test results, and other health-related data.
They provide healthcare providers with an efficient and secure way to manage patient records, enable seamless coordination between various healthcare providers, and ultimately improve patient care.
However, with the convenience of EMRs come security concerns that can lead to unauthorized access, theft, or misuse of protected health information. It's essential to implement robust security policies and procedures to protect these valuable data from potential threats.
Electronic Medical Records (EMRs) contain sensitive personal and identifiable health information, making it crucial to establish effective security measures. There are various ways to safeguard EMRs, which are mostly dictated by laws and regulations. Let's take a look at some of these ways.
| Technical Safeguards | Administrative Safeguards | Physical Safeguards |
| Access Control: Ensures only authorized personnel can gain access to EMRs through authentication methods like passwords or PINs. | Setting up policies, procedures, and guidelines to ensure compliance with regulations and laws that protect EMRs. | Securing the physical devices that store EMRs by implementing measures like firewalls, antivirus software, and endpoint management tools. |
| Audit Controls: Tracks and records all access and modifications to electronic health records to detect security incidents or breaches. | Implementing training programs to educate healthcare providers and administrative staff on security risks and appropriate responses. | Installing safeguards such as firewalls, antivirus software, and endpoint management tools to oversee and secure electronic devices that store EMRs. |
| Integrity Controls: Limits access to specific fields of records, allowing authorized personnel to make changes and ensuring information accuracy. | ||
| Transmission Security: Safeguards the transmission of EMRs, ensuring secure and encrypted transfer of data to prevent unauthorized access. | ||
| In conclusion, safeguarding EMRs is vital, and a multi-faceted approach is necessary. Employing technical, administrative, and physical safeguards ensures optimal security for electronic medical records. |
Cybersecurity threats continue to rise, and businesses must be extra vigilant in safeguarding their electronic medical records. Unprotected electronic devices could be an easy target for cybercriminals who could exploit any vulnerability. One crucial step towards securing EMRs is the use of antivirus software. However, failing to implement reasonable measures to protect these valuable records could lead to serious legal and financial repercussions. In this article, we'll delve into the importance of antivirus software and the potential risks that come with not encouraging employees to use it.
In today's fast-paced and digital world, electronic medical records (EMRs) have become an essential tool for healthcare providers to manage patient care. However, the use of EMRs comes with some security concerns, such as the potential for cybersecurity breaches and unauthorized access to patient records.
One of the most effective ways to protect against these threats is by ensuring that employees use antivirus software.
Encouraging employees to use antivirus software is essential because it helps protect against various types of malware that could infect the system. Without antivirus software, an organization's network becomes vulnerable to cyberattacks, and it's only a matter of time until an attack happens. Malware can range from simple viruses to more sophisticated spyware, ransomware, and other malicious software that can wreak havoc on an organization's system.
Neglecting this critical security measure can lead to dire consequences, including the compromise of sensitive patient data, financial loss, and legal liabilities. Imagine a scenario where a hacker infiltrates an organization's system and steals personal health information (PHI) from patient records.
This could result in reputational damage, the loss of public trust, and potential lawsuits. The lack of antivirus software could make the organization liable for the breach, leading to severe financial penalties and legal fees.
Other ways to protect EMRs from cyberattacks without antivirus software include restricting access to patient records, implementing role-based access controls (RBACs), and enforcing strict protocols for data handling.
Healthcare companies can also develop robust security policies and procedures for employees to follow or invest in employee training programs to increase their cybersecurity knowledge and awareness.
Healthcare companies can implement notable security techniques to safeguard patient information. These techniques include regular security risk assessments, two-factor authentication, encryption of sensitive data, and regular software patching and updates.
Healthcare companies can also consider appointing a Chief Information Security Officer (CISO) to manage the organization's security risks and ensure compliance with relevant security regulations.
| Reason | Description |
| Lack of Awareness | Some organizations may not fully understand the importance of cybersecurity and the potential risks associated with data breaches. This can lead to a lack of prioritization for security measures. |
| Budget Constraints | Implementing robust cybersecurity measures can be expensive. Smaller healthcare organizations, in particular, may struggle to allocate sufficient funds towards cybersecurity. |
| Complexity of Healthcare Data | Healthcare data is complex and diverse, ranging from patient records to billing information. This complexity can make it challenging to implement effective security measures. |
| Legacy Systems | Many healthcare organizations still rely on outdated systems that may not be compatible with modern security measures. Upgrading these systems can be costly and time-consuming. |
| Regulatory Challenges | The healthcare industry is heavily regulated, and these regulations can sometimes make it difficult to implement new security measures. |
| Lack of Skilled Personnel | There is a global shortage of skilled cybersecurity professionals. This can make it difficult for healthcare organizations to find and retain staff who can implement and maintain effective security measures. |
| Rapid Technological Changes | The pace of technological change can make it difficult for healthcare organizations to keep up with the latest security threats and the measures needed to counter them. |
Protecting electronic medical records is a shared responsibility between healthcare providers, business associates, and patients themselves, with the major goal of ensuring that personal health and medical histories remain confidential.
Given the potential threats and security concerns in the healthcare operations, not having a security policy in place can lead to serious security incidents and put patient privacy at risk. In this article, we'll explore notable security techniques, prominent security methods, and security regulations that healthcare organizations can adopt to protect electronic medical records.
Having a security policy in place is crucial for protecting individuals' personal health information (PHI) against potential threats. Unfortunately, many healthcare providers or organizations still neglect the importance of implementing a comprehensive security policy, which could lead to severe consequences.
One of the most notable consequences of not having a security policy in place is the loss of patient data. This could result in identity theft, financial loss, and reputational damage to the healthcare provider or organization. Patients' identifiable health information, including their medical histories, needs to be safeguarded against unauthorized access or disclosure. Without a strict security policy in place to ensure the confidentiality and privacy of patients, the healthcare provider risks losing the trust of its patients and damaging its reputation.
The absence of a clear set of guidelines for employee behavior exposes the organization to malicious insider activities, such as data theft or sabotage. Without strict security policies in place, employees may unintentionally or intentionally cause a security incident, putting patient data at risk.
If an organization is caught neglecting its security obligations, it may face serious legal and financial consequences. Negligence regarding patients' private information can result in significant regulatory fines and criminal penalties. Healthcare providers should take note of the significant financial and legal repercussions that may arise from failing to safeguard their patients' confidential information.
Electronic medical records, or EMRs, hold valuable information about patients' health histories and personal details. With this in mind, it's imperative that healthcare providers implement an effective security policy to ensure that this sensitive information remains confidential and secure. Here are some essential elements to consider when creating a security policy for EMRs.
To ensure that all relevant points are covered, the top five most relevant keywords that should be included in your security policy for EMRs are Security Policy, EMRs, Privacy and Security, Employee Responsibilities, and Training Requirements.
As healthcare providers store more patient information electronically, security has become a top priority in the industry. Failing to protect electronic medical records can have devastating consequences for patients, healthcare providers, and the industry as a whole.
While there is no perfect solution, taking proactive measures can help reduce the impact of security incidents. In this article, we will discuss one significant way to safeguard electronic medical records: monitoring access to patient records.
Specifically, we will discuss why healthcare providers should monitor access to patient records, what happens when access is not monitored, and the risks and consequences of not monitoring access to patient records.
With the rise of digital threats and data breaches, it has become more important than ever to protect electronic health information from unauthorized access.
One way to safeguard electronic medical records is to monitor the types of access that individuals have when it comes to patient data. This includes every type of access, including those made by employees, business associates, and third-party vendors. By monitoring these accesses, healthcare organizations can ensure the protection of patient privacy and compliance with HIPAA regulations.
One type of access that healthcare organizations must monitor is unauthorized access attempts. These attempts could come from either within the organization or from external sources. Hackers or malicious entities could attempt to gain access to patient data, putting patient privacy at risk and jeopardizing the security of the entire organization.
Another type of access that healthcare organizations should monitor is potential breaches or security incidents. Even with the best security safeguards in place, there is always a risk of a breach occurring. By monitoring access attempts and data usage, organizations can quickly detect any unusual or suspicious activity and take immediate action to rectify the situation.
Finally, healthcare organizations should monitor who is accessing specific data and when. This information can help identify potential security issues. By having a record of who accessed patient data, the organization can verify if access was authorized and take action if an unauthorized person accessed the data.
To maintain HIPAA compliance and ensure the protection of electronic medical records, healthcare organizations should implement role-based access control, multi-factor authentication, and patient privacy monitoring systems. These solutions will help monitor access attempts, identify and prevent security incidents, and ensure that only authorized individuals have access to patient data.
When it comes to patient privacy and the security of electronic medical records, access monitoring is an essential component for maintaining HIPAA compliance. However, there are common mistakes that healthcare companies make when it comes to monitoring access to patient records, which can leave sensitive information vulnerable to unauthorized access.
One common mistake is granting unnecessary access to employees who do not need to view patient records. Giving employees more access than required creates a higher risk of data breaches, as it increases the number of individuals who have access to sensitive information. Therefore, it's advisable to implement role-based access control, which limits employee access to specific patient records based on their job functions.
Another issue that healthcare companies face is a lack of role-based access control. Without proper role-based access control, employees could easily access sensitive information that they shouldn't have access to, creating a legal and ethical problem. To prevent this, healthcare companies should establish protocols that limit access to patient records based on each employee's job function.
A further mistake that companies can make is overlooking temporary worker access or third-party vendor access. Temporary workers and third-party vendors often have the same level of access as employees, which can pose a significant risk. Sometimes companies fail to revoke access when an employee or third-party vendor's contract ends or when temporary workers leave the organization. Failure to revoke access control can lead to inadvertent privacy breaches.
In accessing electronic medical records, healthcare organizations must implement solutions that ensure that patient data is protected and secured. There are different solutions available for ensuring proper access controls are implemented on patient records.
This solution means that access to patient records is based on the employee's role within the organization. By using RBAC, healthcare organizations can control access to patient information and ensure that only those with a legitimate need to access the data can do so.
Technical safeguards provide an added level of security that helps to ensure that patient data is protected from unauthorized access. Firewalls, for example, monitor and filter incoming and outgoing traffic to prevent unauthorized access to the network. Encryption, on the other hand, protects data from being intercepted and accessed by unauthorized parties.
Healthcare organizations can provide training to employees on the importance of protecting patient data and monitoring access to patient records. This training can help employees to understand the importance of adhering to data protection policies and procedures, enabling them to take the necessary steps to safeguard patient records.
Such as two-factor authentication, to prevent unauthorized access to patient records. Two-factor authentication requires users to provide two forms of identification before being granted access to patient records. This system provides an extra layer of protection against unauthorized access by requiring an additional step to authenticate the user.
This solution ensures that any third-party vendors handling patient data are adhering to the same data protection measures as the healthcare organization. By implementing third-party vendor risk management, healthcare organizations can ensure that patient data is protected even when it's being handled by external third-party vendors.
Data privacy and confidentiality are crucial in the healthcare industry, especially when dealing with electronic medical records, as they contain sensitive patient information that should be protected from unauthorized access or disclosure.
Not educating employees on data privacy and confidentiality laws can lead to significant security breaches, legal penalties, and damage to the reputation of healthcare organizations.
One of the most well-known data privacy laws in the healthcare industry is the Health Insurance Portability and Accountability Act (HIPAA). HIPAA sets national standards for protecting the privacy and security of patients' identifiable health information and holds healthcare providers accountable for safeguarding such information.
In addition to HIPAA, the Health Information Technology for Economic and Clinical Health (HITECH) Act added new requirements for HIPAA compliance and strengthened the penalties for non-compliance.
If employees are not familiar with these laws, they may not know the significance of their roles in protecting patient information and may act in ways that compromise data privacy and confidentiality.
For example, a healthcare employee who mistakenly discloses a patient's medical history to an unauthorized individual could face criminal penalties and could also damage the reputation of their organization.
To mitigate these risks, it is important to train employees on data privacy and confidentiality laws regularly. This can involve providing refresher courses on HIPAA and HITECH, as well as incorporating simulations to test employees' understanding of the laws and their ability to put them into practice.
It is also important to ensure that employees have access to educational resources on these laws, such as online courses or informational materials, so they can refer back to them as needed.